UK AI Institute: AI cyber capabilities double every 4.7 months
Serge Bulaev
The UK AI Safety Institute reports that AI models' cyber capabilities may be doubling every 4.7 months since late 2024. Their tests suggest these models can now solve more complex cyber tasks much faster, though real-world conditions might be harder. This fast progress may mean defenders need to update their security much more often, not just once a year. The institute notes that no single test proves attackers' success, but the speed of improvement suggests early and strong defenses are needed. Future experiments with tougher tests and active defenders might change how security teams prepare.

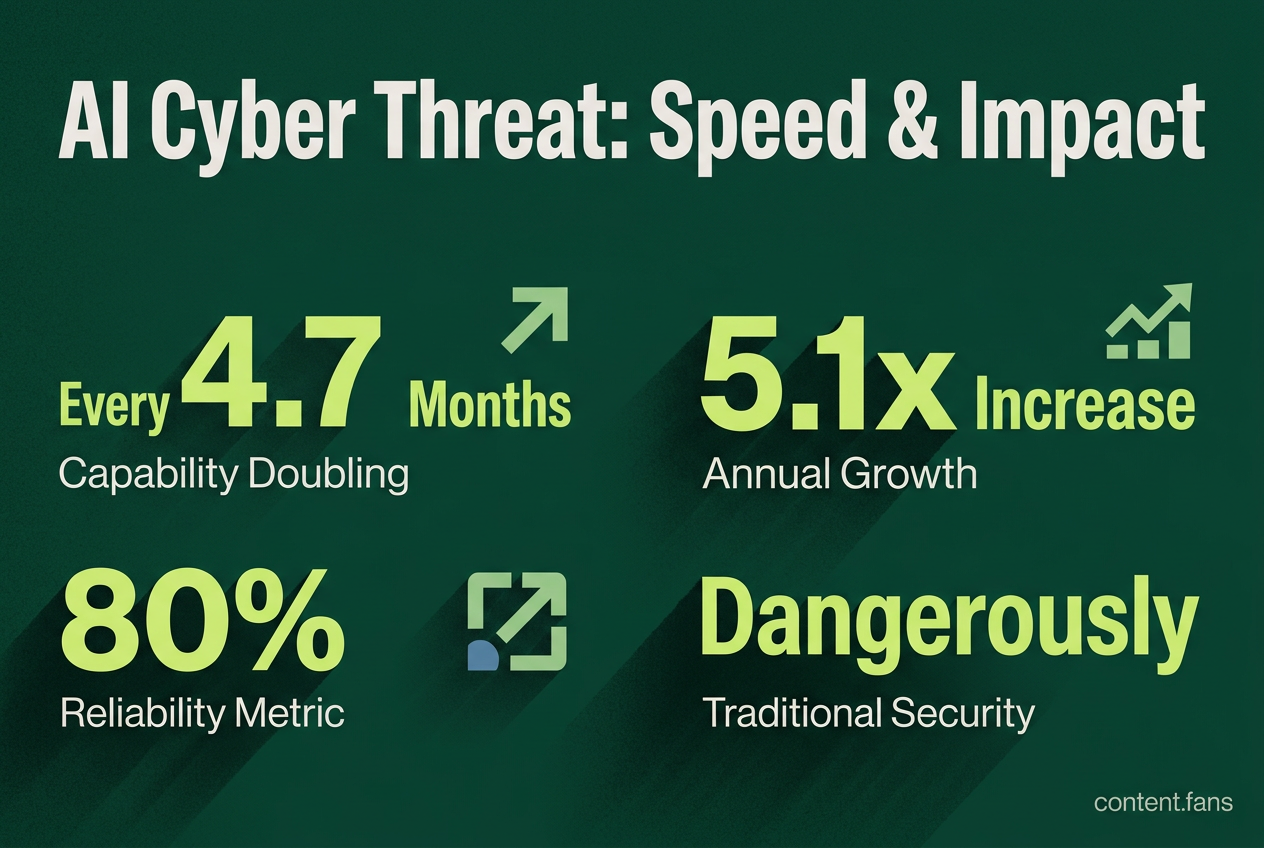
A landmark report from the UK's AI Safety Institute (AISI) indicates that autonomous AI cyber capabilities are doubling approximately every 4.7 months. This rapid advancement means AI models can solve increasingly complex cyber tasks with growing reliability, fundamentally compressing defense timelines. Security planners must now adapt to a reality where an attacker's toolkit may evolve multiple times within a single traditional annual security cycle.
What Is the "Cyber Capability" Being Measured?
AISI's '80%-reliability cyber time horizon' is a time-horizon metric describing how long a cyber task can be and still be completed with 80% reliability in the evaluation setup. This horizon of reliable capability is what has been doubling every 4.7 months.
In its tests, AISI benchmarked successive AI models against capture-the-flag challenges and multi-step cyber ranges. According to the institute's blog post, the task length that models could reliably finish doubled every 140 days (AISI). Recent models like Claude Mythos Preview and GPT-5.5 have even exceeded this trend line. While AISI cautions that these tests lack active human defenders, the findings align with independent measurements, suggesting the trend is robust.
Why This Rapid Growth Compresses Defender Timelines
A doubling rate of 4.7 months means about a five-fold increase in capability in one year (roughly 5.1x). This pace renders traditional security postures, such as annual penetration tests and quarterly patch cycles, dangerously obsolete. As analysts noted in Help Net Security, this compression points toward a need for near-continuous control validation instead of periodic audits.
This pressure is especially acute for critical infrastructure operators in energy, water, and transport, where legacy Operational Technology (OT) is difficult to patch. Advanced autonomous AI can chain misconfigurations across IT and OT networks, conduct reconnaissance at machine speed, and execute multi-stage exploits that previously required human expertise.
What Critical Infrastructure Teams Should Do Now
While the tests do not guarantee an attacker's success in a real-world environment, the speed of progress demands immediate, proactive defense. AISI recommends that organizations prepare for shorter intruder dwell times and a higher volume of automated attacks. The focus must shift from periodic checks to continuous hardening.
Key defensive actions include:
- Shrink the Attack Surface: Immediately remove unused remote access paths, default credentials, and unnecessary OT jump hosts.
- Harden Identity: Enforce phishing-resistant multi-factor authentication (MFA) and just-in-time privileged access to counter AI-accelerated credential abuse.
- Automate Exposure Management: Deploy automated detection and continuous control validation tools that can keep pace with the threat's evolution.
- Segment Networks: Strictly segment OT from IT to prevent lateral movement from less-secure enterprise systems.
- Rehearse for AI-Speed Incidents: Update incident response plans and tabletop exercises to assume attackers can achieve goals in minutes or hours, not days or weeks.
As AISI and other labs continue to conduct more advanced experiments with active blue teams, the planning horizon for security teams will only continue to be refined. The core message is clear: the era of annual security planning is over, replaced by a need for continuous, automated, and adaptive defense.