Fin AI outlines compliance for agent-driven financial workflows
Serge Bulaev
Banks, hospitals, and law firms are starting to use autonomous agents in their systems, but this may create new compliance challenges with overlapping rules and penalties. Fin AI says U.S. banks using agents for credit scoring must document their models, while the EU AI Act appears to require transparency and human oversight by August 2026. Experts suggest keeping detailed, secure logs and limiting agent access to only what is needed. Case studies suggest that adding governance does not have to slow down work, and teams might use performance metrics to keep compliance controls up to date as rules change.
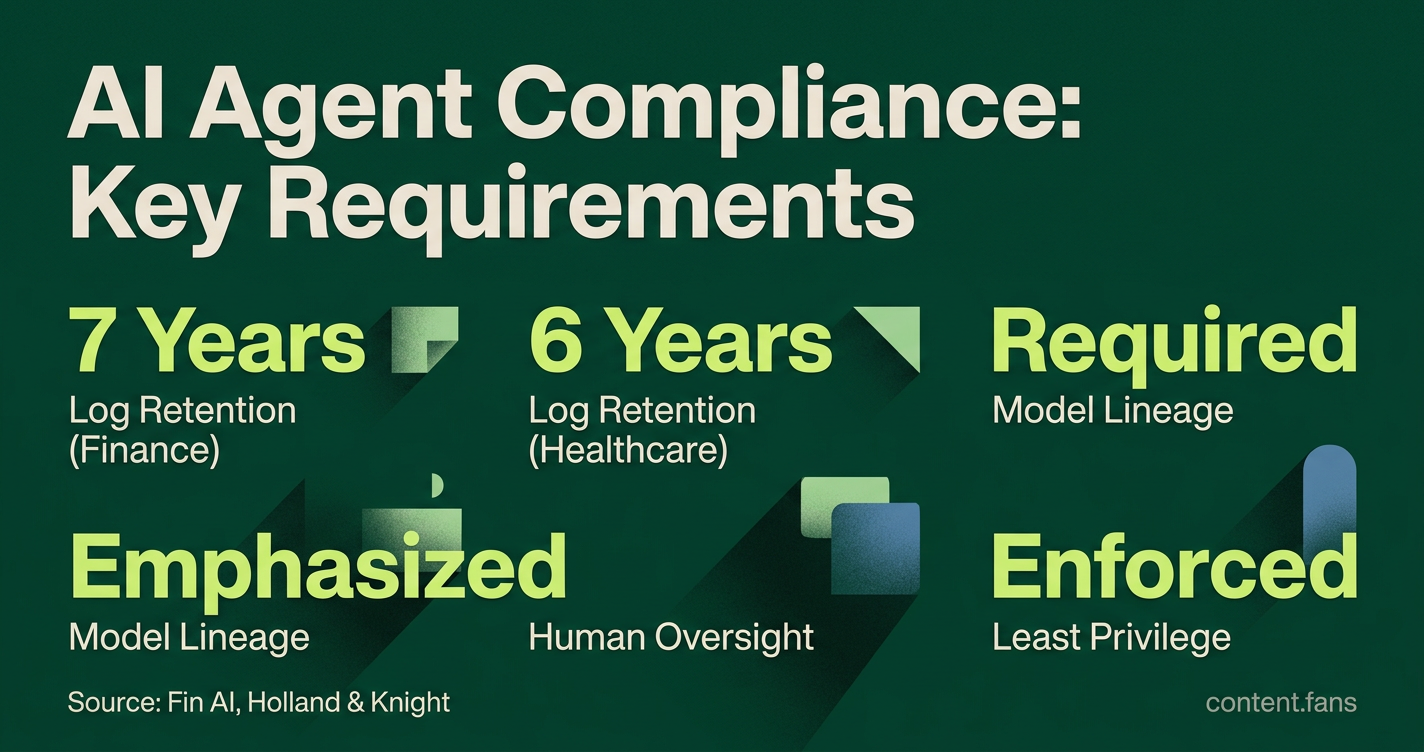
Managing compliance for agent-driven financial workflows is now a critical priority for organizations integrating autonomous AI. As banks, hospitals, and law firms adopt these agents, they navigate a complex landscape of overlapping regulations and severe penalties. Teams must address a growing governance surface while proving control over agent actions. For instance, according to industry reports, banking regulations increasingly require documented model lineage for AI credit scoring, while emerging AI regulations emphasize transparency and human oversight requirements Fin AI.
Understand the Regulatory Landscape Before Development
Each regulated sector - finance, healthcare, and legal - faces unique AI compliance rules and enforcement models. For example, a significant number of state-level AI in healthcare bills have emerged recently, emphasizing patient consent and clinician accountability Holland & Knight. Banking regulators demand extensive validation reports for all model updates, while new laws in various jurisdictions for legal bots enforce strict AI disclosure requirements and penalties.
To ensure compliance, teams must first analyze all applicable regulations across jurisdictions. The next step involves engineering systems for immutable audit logging and enforcing least-privilege access for each agent. Finally, integrate these controls into real-world workflows and continuously monitor performance against key compliance metrics.
Engineer Systems to Generate Verifiable Evidence
Audit logging is the foundational control for regulatory review. Systems must produce immutable, encrypted logs integrated with a Security Information and Event Management (SIEM) tool, with retention periods often set at seven years for finance and six for healthcare. Equally critical is enforcing the principle of least privilege, where each agent's access is strictly limited to the tools and data essential for its designated function.
- Log Everything: Record all prompts, responses, and tool interactions, ensuring sensitive data is sanitized.
- Ensure Integrity: Cryptographically sign logs and store them in immutable, write-once storage.
- Control Access: Implement role-based access control (RBAC) specific to agent versions.
- Secure Identities: Automate secret rotation and isolate agents in dedicated identity domains.
- Monitor Behavior: Use anomaly detection to flag unusual agent activity in log streams.
Implement Governance Within Live Workflows
Integrating compliance controls does not need to impede operational efficiency. For example, according to industry reports, major financial institutions have achieved significant time savings in contract reviews by implementing human oversight and clear decision documentation. Similarly, leading healthcare organizations have successfully validated their clinical support agents by embedding continuous monitoring and HIPAA-compliant data governance, proving a clear audit trail from prediction to source data.
Measure and Iterate on Compliance Controls
A compliance-first architecture transforms static checklists into dynamic, living controls through continuous measurement. Key performance indicators (KPIs) should include log coverage, data integrity, contextual richness, and anomaly detection rates. Teams should establish baseline metrics during pilot programs and iteratively adjust them as new regulations introduce additional requirements.
What makes audit logging for AI agents different from traditional logs?
Traditional app logs capture system state - HTTP codes, stack traces, memory spikes.
Agent logs must capture the triple-identity (user + agent version + exact tool) and the cognitive path: every prompt, reasoning step, tool call, and the policy evaluation that allowed it.
According to industry reports, regulators increasingly expect cryptographically signed, immutable decision traces so that when an auditor asks "why did the agent reject this loan?" you can replay the entire chain back to the training data hash.
Which upcoming deadlines should financial-services agents meet?
- EU AI Act high-risk list - High-risk systems (including credit-scoring) must have adequate risk assessment, high-quality datasets, logging, detailed documentation, and human oversight measures by August 2, 2026.
- Emerging state regulations - Various jurisdictions are implementing requirements for agents that materially affect consumer financial products to complete algorithmic impact assessments and file disclosures.
Miss these deadlines and fines can reach significant portions of global turnover.
How do you enforce least-privilege access on an autonomous agent?
Start with role-based micro-permissions: each agent identity gets its own scoped API token that can invoke only the tools listed in its governance card.
According to industry best practices, organizations should implement automatic secret rotation and tenant-isolated identity domains so that a breach in one agent cannot be escalated to downstream ledgers.
Log every authorization decision in real time; if an agent suddenly attempts to access a SWIFT terminal it has never touched, the SIEM should kill the session within seconds.
What real evidence exists that compliant agents actually save money?
According to industry reports, major financial institutions have achieved substantial time savings in legal document review while still satisfying model-risk rules.
Healthcare organizations have reported significant reductions in audit cycles and errors after agents began continuously classifying data-access events.
Across multiple pilots, firms that baked governance-by-design into agent workflows recouped the implementation cost within a small number of audit cycles.
How do you prepare for a regulator's very first "agent inspection"?
- Build a model registry that maps every deployed agent to its training-data version, bias-test report and human-approval gate.
- Export immutable decision traces (7-year retention is now the default for FinServ).
- Have a red-team summary ready; industry reports note that examiners routinely ask for recent adversarial-prompt findings and the patches applied.
- Show vendor SLAs that guarantee timely access to model cards - this is considered a key way to prove "reasonable care" under emerging regulations.