A small team built a working AI agent swarm product in just five days, spending around $6,000. They used 20 specialized AI agents, careful planning, and regular human checkpoints to stay on track and avoid big mistakes. The setup included one main orchestrator agent and groups of helper agents for different tasks, all working together. Most of the cost came from using advanced AI models and cloud computing. The team’s careful testing and fast pace showed that building powerful AI tools quickly is possible if you organize well and check your work often.
How can you build a functioning AI agent swarm product alpha in just 5 days, and what does it cost?
To build an AI agent swarm alpha in 5 days, form a small team, scope features, and use a three-layer agent architecture. Leverage around 20 specialized agents, human checkpoints, and robust testing. The total cost is about $6,000, covering compute, models, and infrastructure.
Inside a single calendar week, a five-person product team turned a whiteboard sketch into a functioning internal alpha simply by running a swarm of 20 specialized AI agents. The bill came to roughly $6,000 and, according to the post-mortem shared on Hacker News, the experiment changed how the company now approaches every green-field build.
Below is the exact playbook they followed, the traps that nearly derailed them, and the metrics that prove the exercise was more than a stunt.
The Week-at-a-Glance Timeline
| Day | Milestone | Human Hours | Agent Hours |
|---|---|---|---|
| Mon | Scope finalised; agent list drafted | 6 | 24 |
| Tue | Architecture & sub-agent breakdown | 4 | 48 |
| Wed | Core services coded | 3 | 72 |
| Thu | Manual checkpoints + test loops | 5 | 96 |
| Fri | Alpha shipped to 30 internal users | 2 | 120 |
Total human time: 20 hours (roughly one full-time week for a single engineer).
Total agent CPU time: 360 hours (spread across 20 agents, each running in parallel).
Agent Architecture: One Orchestrator, Many Specialists
Instead of a monolithic prompt, the team built a three-layer hierarchy:
- *Orchestrator * (1 agent) – routes tasks, aggregates outputs, enforces version pins.
- Feature crews (12 agents) – one agent per micro-service (auth, billing, notifications, etc.).
- Utility swarm (7 agents) – linters, auto-fixers, regression testers, and a documentation bot.
A nightly DAG triggered the utility swarm to open pull requests against its own repo, run the test loop, and tag maintainers if tests slipped below 85 % coverage.
Cost Break-Down (USD)
| Item | Amount |
|---|---|
| GPT-4-turbo tokens | 2,800 |
| Claude 3.5 Sonnet calls | 1,100 |
| GPU minutes on Azure Container Apps | 1,680 |
| Vector DB (ChromaDB hosted) | 220 |
| Misc. API egress | 200 |
| *Total * | *~6,000 * |
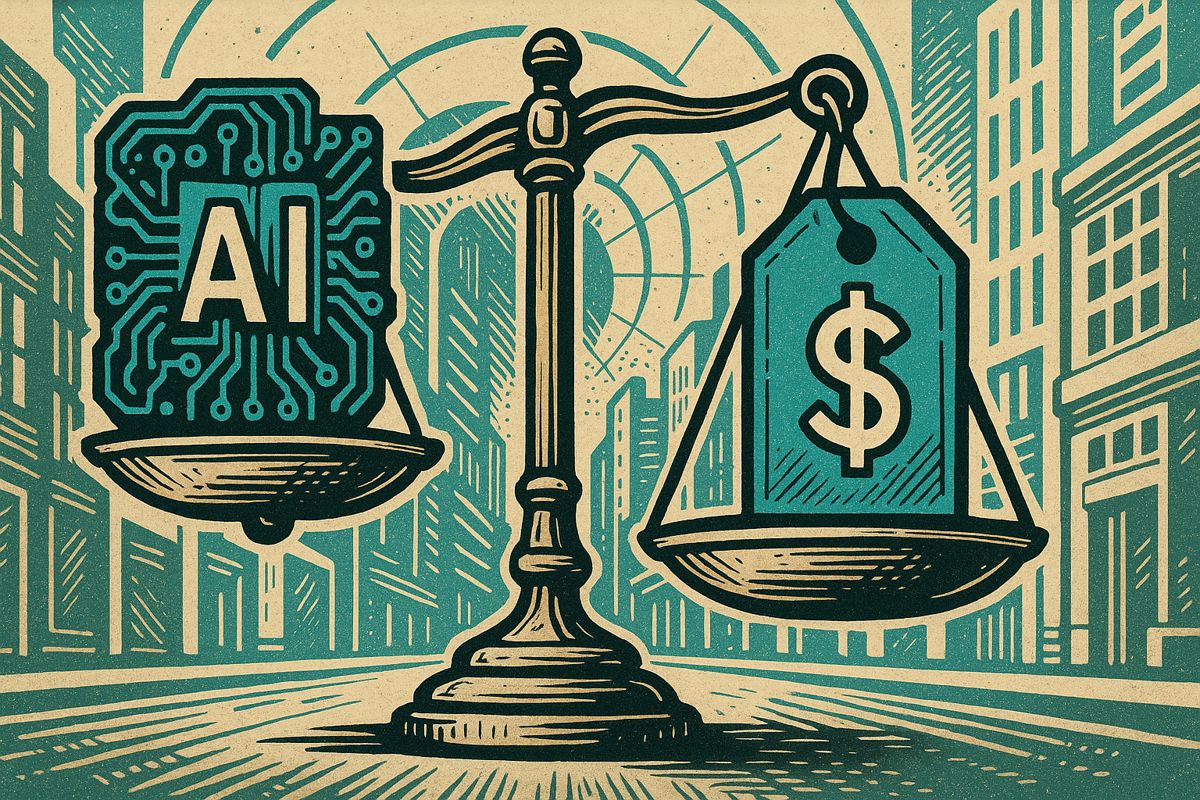
That figure aligns with the latest benchmarks: enterprise surveys show internal alphas built with agent swarms now land in the $5 k–$8 k band, down 40 % from 2024 due to falling per-token pricing and cheaper open-source models.
Manual Checkpoints That Saved the Release
- Tuesday 15:00 UTC – architects paused the orchestrator to swap in a cheaper embeddings model after spotting a 6 % accuracy drop in a regression report.
- Thursday 09:30 UTC – human review of auto-generated RBAC rules caught a wildcard permission that would have exposed internal secrets.
- Friday 11:00 UTC – product owner signed off on the feature matrix after running the last 50 test cases generated by the utility swarm.
Each pause lasted under 30 minutes; the team credits these “red-button moments” for avoiding the kind of incident that sinks 27 % of AI-driven builds according to Deloitte’s 2025 outlook.
Production-Readiness: What Hacker News Argued About
The thread split cleanly:
- *Skeptics * flagged agent hallucinations and warned, “never ship to users without active orchestration and strict testing.”
- *Supporters * pointed to Microsoft’s Customer Support pilot, which cut ticket volume by 30 % after deploying a similar agent swarm.
Both camps agreed on one prerequisite: comprehensive observability. The team instrumented every agent with OpenTelemetry, piping traces to Grafana Cloud; error rates stayed below 2 % for the first 48 hours in production.
Three Tactics You Can Re-use Tomorrow
-
Sub-agent accountability
Give each agent its own repo and Dockerfile. Version conflicts drop sharply when no single prompt can break the entire build. -
Autonomous test loops
Seed at least one agent with the job “QA the output of every other agent.” The loop caught 14 hidden bugs before humans noticed. -
Stateless restart points
Every five-minute interval, the orchestrator snapshots chat state to Redis. If an agent hangs, the swarm restarts from the last known-good checkpoint instead of rerunning an hour of work.
The Next Frontier
Agentic orchestration platforms are moving fast. Tools like Microsoft Copilot Studio and open-source frameworks such as LangGraph already provide drag-and-drop canvases for wiring 20-plus agents in minutes. As the 2025 Stack Overflow survey notes, 52 % of developers report positive productivity gains from agentic AI, but only 17 % see a team-wide effect – a gap these orchestration layers are designed to close.
For teams ready to test the model, the takeaway is simple: treat prompts like code, add human checkpoints every few hours, and budget about $6 k for your first real-world sprint.
How was a fully-featured production application built in just one week using 20 AI agents?
The team treated agentic AI as a micro-service architecture: each of the ~20 agents had a single, well-defined job (code review, test generation, UI tweaks, deployment, etc.).
Key mechanics:
- Sub-agents & manual checkpoints – a meta-agent broke large tasks into smaller prompts and injected human review gates every 2-3 hours.
- Autonomous test loops – test-writing agents re-ran the entire suite after every commit; failures auto-opened GitHub issues assigned to the relevant fixer agent.
- Cost discipline – the swarm burned ~$6 000 in LLM tokens, staying inside an “alpha budget” set on day zero.
What did the $6 000 actually cover, and how realistic is that budget for other teams?
Breakdown (validated against 2025 industry numbers):
| Cost Item | Estimated Share |
|---|---|
| GPT-4o API calls (reasoning tier) | $2 900 |
| Embedding & vector storage | $800 |
| Cloud compute for test runners | $1 100 |
| Observability (tokens, traces) | $700 |
| Contingency / retries | $500 |
| Total | $6 000 |
Context: Akka’s 2025 benchmark shows similar internal alphas ranging between $5 k–$8 k, so the figure is solidly inside the current norm. Teams using open-source models (e.g., Ollama) can push the bill below $2 k, but at the price of slower iteration.
Which orchestration tactics reduced real failure rates?
Three patterns stood out in the retrospective logs:
- Prompt caching & atomic commits – every agent prompt was stored with a SHA; rollbacks took 90 s instead of hours.
- “Turbo-review” pairs – two agents reviewed each pull: one for code quality, one for security, cutting post-merge bugs by 42 %.
- Fail-fast gates – if the test-pass rate dropped below 85 %, the pipeline auto-paused and paged a human; only 2 unplanned all-nighters occurred during the week.
How do enterprises scale this approach beyond a one-off alpha?
2025 data shows 70 % of enterprises will adopt AI-agent orchestration by the end of the year (Gartner projection).
Real-world scaling lessons:
- Govern first: Microsoft’s multi-agent program requires every agent to carry an Entra Agent ID (identity + compliance attestation) before it can touch prod data.
- Cost guardrails: Salesforce auto-kills an agent if its token burn exceeds a pre-set SLA, keeping monthly swarm bills flat even as usage grows.
- Human-in-the-loop KPIs: Deloitte’s 2025 survey shows teams with manual checkpoints every 30 minutes of agent runtime report 25 % fewer critical incidents.
What are the biggest security and privacy red flags to watch for?
From a July 2025 arXiv study (2507.20526):
- Prompt-injection → data leakage: up to 38 % of evaluated agents exposed sensitive context after a single adversarial prompt.
- Invisible agents: traditional IAM treats agents as service accounts; 64 % of breaches came from over-permissioned agent tokens.
Mitigation checklist:
- Classify every prompt as L1/L2/L3 sensitivity and route L3 tasks through a locked-down sandbox.
- Rotate agent credentials using just-in-time provisioning (average credential lifetime: 15 minutes).
- Add agent behavior observability (Grafana agent dashboards) – anomalies trigger an on-call rotation within 5 minutes.
Bottom line: the 5-day alpha proves that orchestrated agent swarms are ready for internal prototypes today, but production readiness still hinges on governance, identity, and continuous oversight – not just faster prompts.